Classifying Information
Organizations increasingly rely on digital information and information systems to serve the public and fulfill their mandates.
You have an important role in protecting the information you handle and the systems and devices you use.
Not all information and systems are protected in the same way. Identifying what needs to be protected and how is critical to effective cyber security.
Information Security
Information Sensitivity Classification
When it comes to information, one size does not fit all.
Information classification is fundamental to an effective cyber security program.
All information must be evaluated, classified and safeguarded in accordance with its sensitivity level.
| Sensitivity Level | Description |
|---|---|
| High Sensitivity | Unauthorized disclosure could result in loss of life or impact to public safety, significant loss of confidence in or embarrassment to government, extremely serious personal or enterprise injury, major economic impact, sabotage or terrorism, or significant financial loss or social hardship. |
| Medium Sensitivity | Unauthorized disclosure could result in serious personal or enterprise injury, loss of competitive advantage, loss of confidence in a government program, moderate financial loss, or damage to partnerships or reputations. |
| Low Sensitivity | Unauthorized disclosure could result in minor injury to persons, minor financial loss, slight embarrassment, or inconvenience. |
| Unclassified | Disclosure will not result in any harm or injury and does not require prior authorization. |

Information Sensitivity Classification
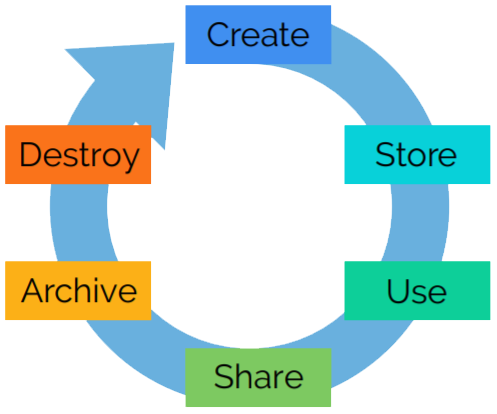
Here are the steps you need to take:
- Classify the information to one of the four sensitivity levels
- Label all information with the appropriate sensitivity level
- Safeguard the information in accordance with its sensitivity level